Security that supports operations
We apply security in ways that protect systems while keeping them usable, manageable, and aligned with how the organisation operates.

What this covers
Cybersecurity is most effective when it is practical, visible, and maintainable.
Access control
Managing accounts, privileges, authentication, and access patterns so access is appropriate and reviewable.
System hardening
Reducing avoidable exposure through configuration, patching, baselines, and secure defaults.
Monitoring and visibility
Improving awareness of activity, changes, alerts, and signals that require attention.
Risk reduction
Prioritising improvements based on impact, effort, operational reality, and long-term maintainability.
Typical enterprise security model
Security usually spans identity, access, network controls, endpoints, monitoring, and response. The value comes from making these layers work together.
Identity
SSO, MFA, directories, conditional access, and identity lifecycle controls.
Access
Role-based access, privileged access management, VPN, and Zero Trust patterns.
Network
Firewalls, segmentation, secure routing, IDS/IPS, and controlled connectivity.
Endpoints & servers
Hardening, EDR/XDR, patching, configuration baselines, and device visibility.
Monitoring
SIEM, log aggregation, event correlation, alerting, and operational visibility.
Response
SOC processes, response playbooks, containment, recovery, and reporting.
How we support your security journey
Security is not a one-off exercise. It involves designing the right controls, validating them over time, and operating them continuously.
Design and implementation
We help design and implement security controls that fit your environment — including SSO, MFA, role-based access, privileged access management, jump hosts, segmentation, and hardening.
Assessment and validation
We carry out targeted assessments to identify gaps, validate controls, and highlight next steps — including vulnerability scanning, exposure reviews, security assessments, and penetration testing coordination.
Ongoing monitoring and support
We operate and support security systems on an ongoing basis — collecting logs, monitoring signals, triaging alerts, and coordinating escalation to SOC partners where required.
Security monitoring and operational response model
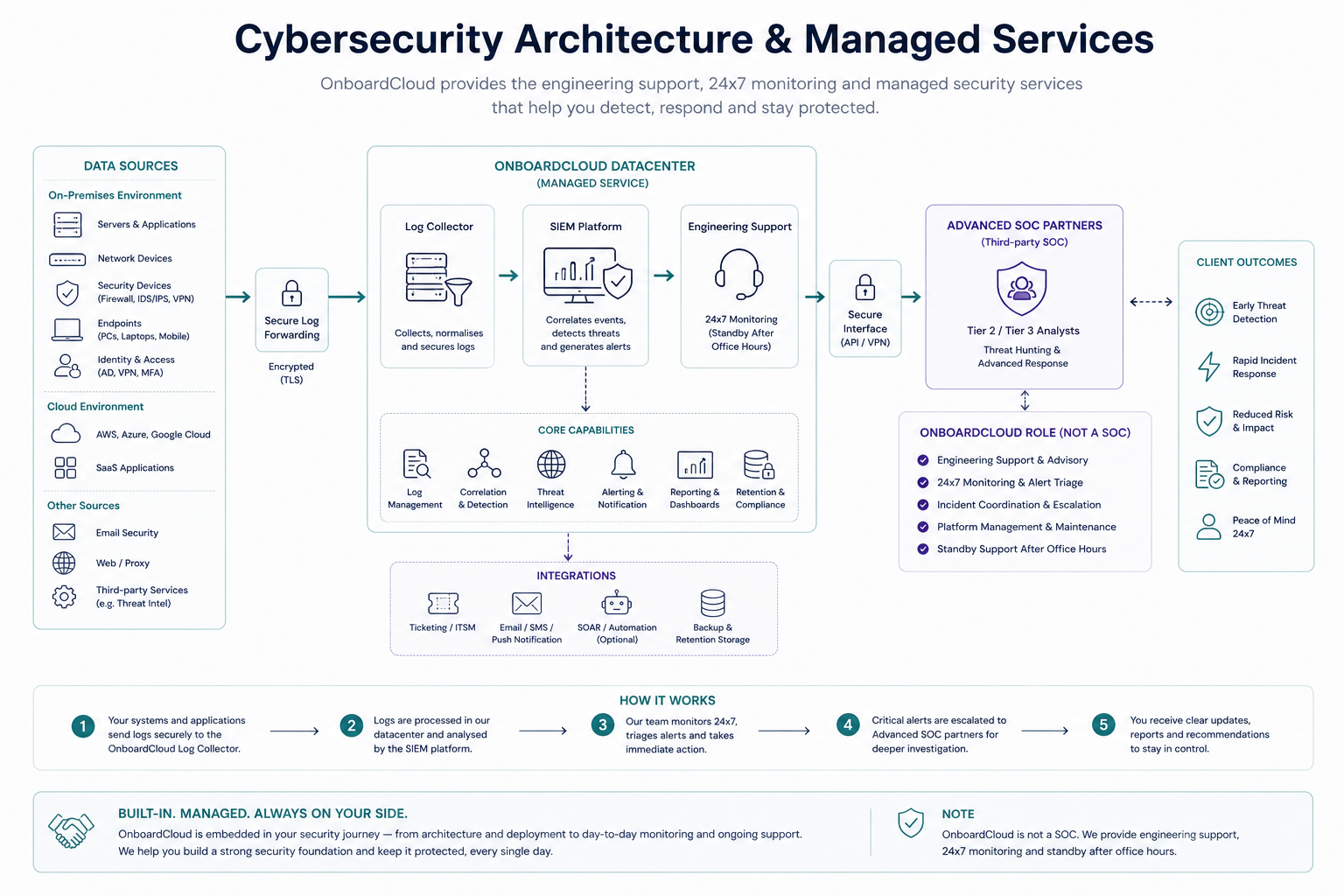
The model below shows how logs and security signals flow through a managed setup — from client environments into OnboardCloud-operated systems, with escalation paths where deeper investigation is required.
OnboardCloud provides the managed engineering layer — including log collection, SIEM platform operation, alert triage, and escalation coordination. Advanced SOC investigation can be integrated where clients subscribe to a third-party SOC service.
How we approach cybersecurity
Security should reduce risk without turning the environment into something difficult to use or maintain.
- Aligned with operations
Controls are designed around how systems are actually used, not only how they look on paper. - Controlled access
We reduce excessive access while preserving the ability to operate effectively. - Visible activity
Security decisions are easier to manage when access, changes, and alerts are understandable. - Practical measures
We focus on controls that can be sustained beyond the initial implementation.
What this means in practice
Security becomes part of how systems are run, rather than a separate layer that is ignored or bypassed.
Lower operational risk
Common gaps are reduced before they become larger problems.
Better accountability
Access and changes can be reviewed and explained.
Less disruption
Controls support day-to-day operations instead of slowing them unnecessarily.
More confidence
Leaders and teams have better visibility into the state of the environment.
Looking to strengthen security?
We can help design, validate, and operate security controls so protection becomes an ongoing capability — not just a one-time project.